Outline VPN is a project of Jigsaw, a subsidiary of Google. Outline uses the Shadowsocks protocol to communicate between client and server. Traffic is encrypted using the IETF ChaCha20 cipher and authenticated using IETF Poly1305.
Deploying Outline VPN on a VDS or your own server is quite simple, the instructions are on the official website of the project:
Outline VPN: Get Started or on Medium
UPD. 17.11.2023 Found a solution for problem below, at the end of the article.
daemon.err /usr/bin/ss-redir[7401]: accept: No file descriptors available
The problem is that there is no official instruction for using Outline on OpenWRT, but since Outline VPN is based on Shadowsocks, we can use Shadowsocks-libev:
shadowsocks-libev-ss-local
shadowsocks-libev-ss-redir
shadowsocks-libev-ss-rules
shadowsocks-libev-ss-tunnelAnd for setup in the LUCI graphical interface
luci-app-shadowsocks-libevInstalling the packages:
opkg update
opkg install shadowsocks-libev-ss-local shadowsocks-libev-ss-redir shadowsocks-libev-ss-rules shadowsocks-libev-ss-tunnel
opkg install luci-app-shadowsocks-libevThen we’ll need an Outline Access Key
Open Outline Manager

Add a new key or use an existing one
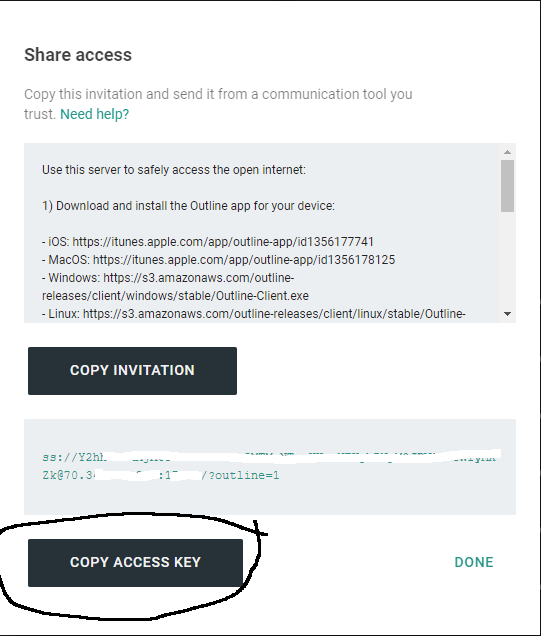
We copy the access key, it contains the IP address of the server and the connection port and password in encrypted form
ss://[password-encrypted]@IP:Port/?outline=1
Further on the example of LUCI (OpenWRT 19.07)
Go to the Services — Shadowsocks-libev
Go to Remote Servers
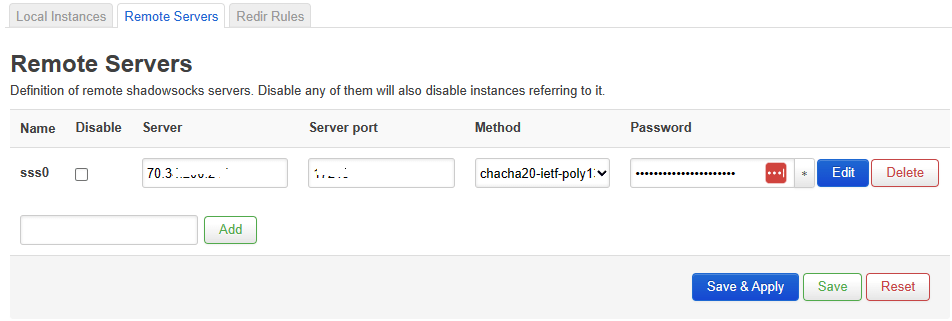
Here we insert the IP address, port of the Outline server and a password
To get the password, you need a Base64 decoder, for example Base64 Decode and Encode — Online
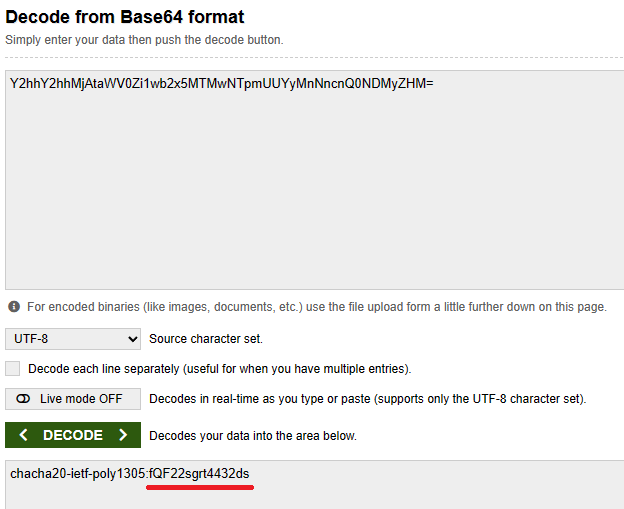
We insert the decrypted password and select the desired encryption method from the drop-down list, and then uncheck the Disable field.
Applying Changes
In the current version of OpenWRT, in the Remote Servers section, there is an Import link option, where we simply paste our access code from Outline and get a ready-made entry in the config.

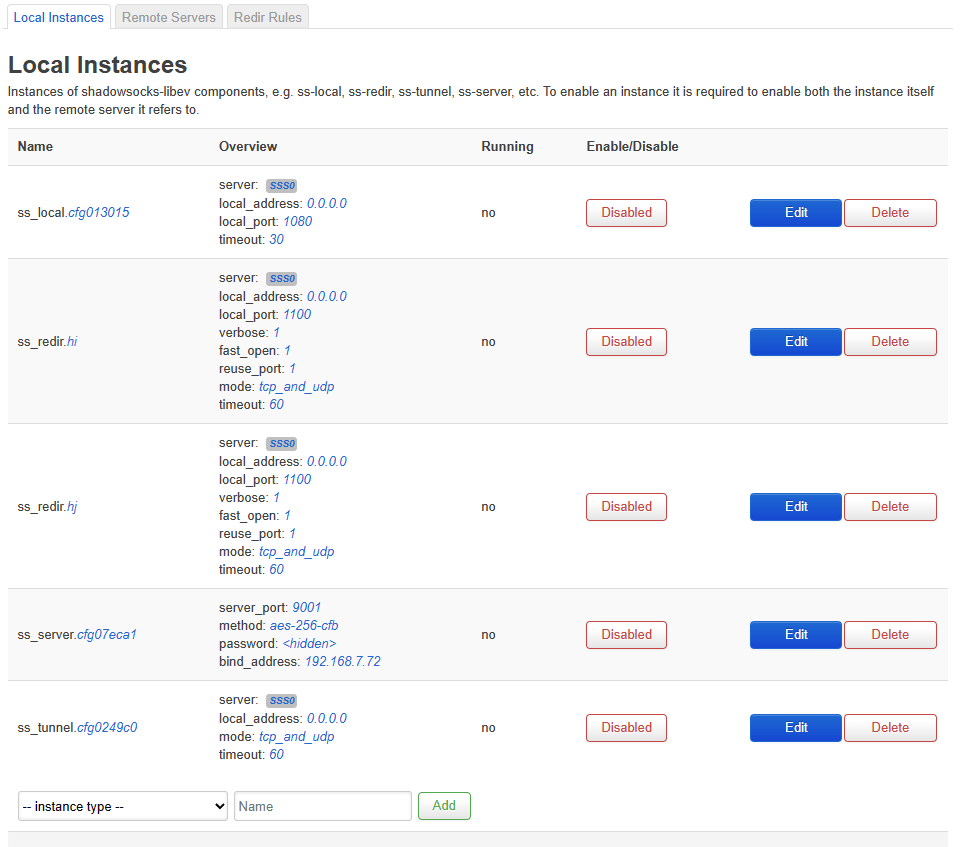
Next, return to the Local Instances tab

Here we see the templates created by default, we need the ss_redir template
First, let’s go to ss_redir.hj (or ss_redir.hi or you can create a new one, it doesn’t matter)
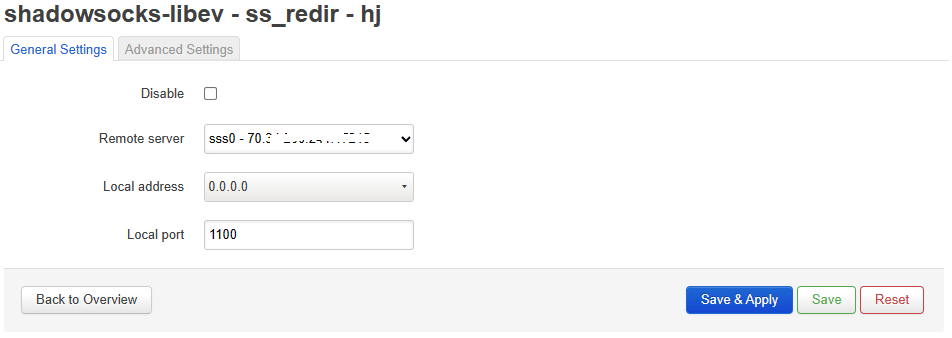
We check that there is a server with Outline data in the Remote Server column, uncheck the box next to Disable
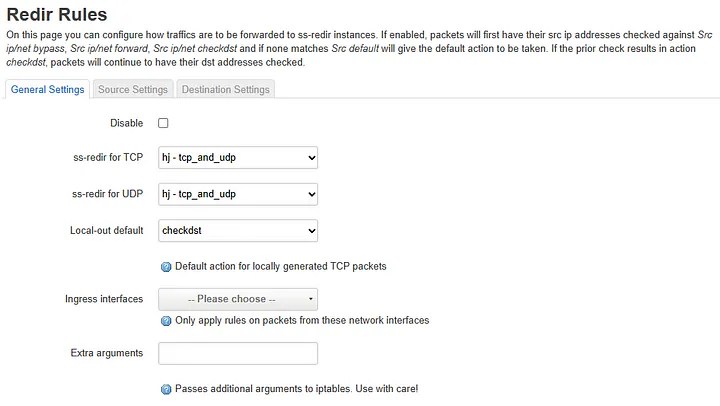
Next, go to the Redir Rules tab
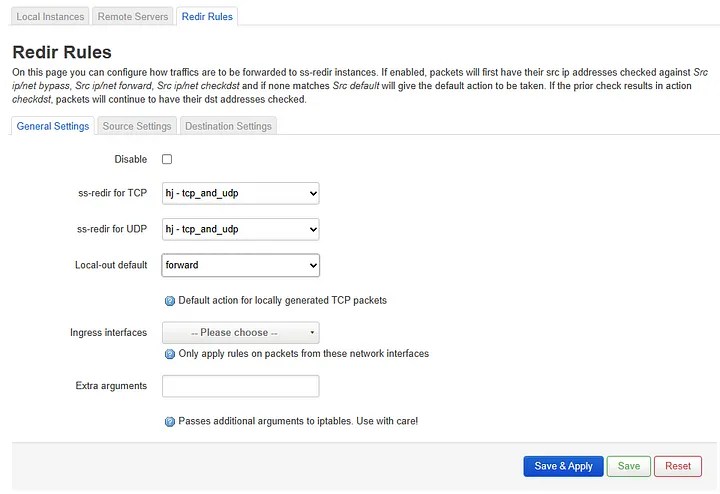
Check that ss-redir for TCP and UDP matches the previously selected item (hj, hi or the one you created)
By default, all traffic will go through a proxy, so leave the forward option, make sure that there is no checkbox next to Disable and go to the Source Settings tab
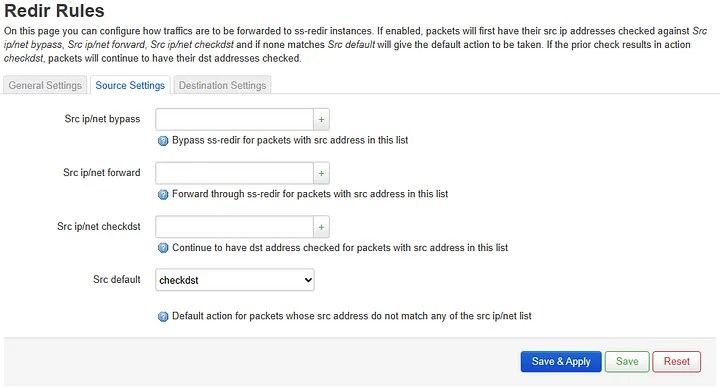
Here we leave the default parameters, then go to Destination Settings
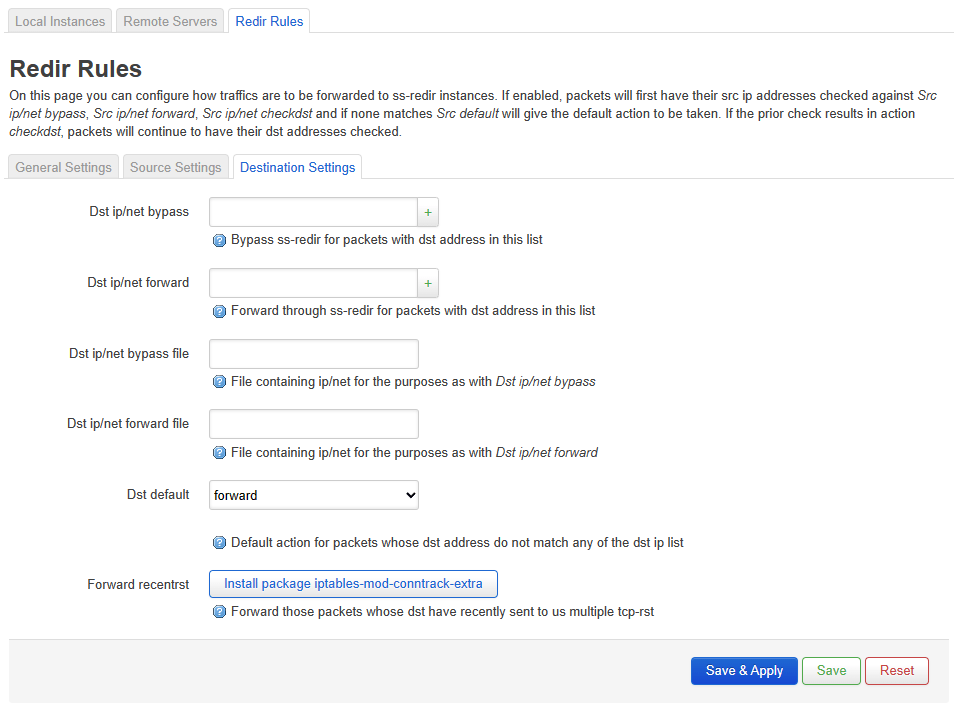
Here we set for default Dst — forward (by default, all traffic will go through a proxy, other options will be at the end of the article)
Click Save&Apply and check if its working.
This is how the /etc/config/shadowsocks-libev config will look like:
config server 'sss0'
option server '$OUTLINE_IP'
option server_port '$PORT'
option method 'chacha20-ietf-poly1305'
option password '$DECRYPTED_PASSWORD'
config ss_tunnel
option server 'sss0'
option local_address '0.0.0.0'
option mode 'tcp_and_udp'
option timeout '60'
config ss_redir 'hj'
option server 'sss0'
option local_address '0.0.0.0'
option local_port '1100'
option mode 'tcp_and_udp'
option timeout '60'
option fast_open '1'
option verbose '1'
option reuse_port '1'
config ss_rules 'ss_rules'
option src_default 'checkdst'
option dst_forward_recentrst '0'
option redir_tcp 'hj'
option redir_udp 'hj'
option local_default 'forward'
option dst_default 'forward'If desired, you can use Outline only for a list of addresses (for example, antifilter.download lists)
In this case, in the General Settings, change Local-out default from forward to check-dst
In the Destination Settings section, change the default policy Dst default to bypass and add your list of addresses / subnets that should work through a proxy to the Dst ip / net forward file item.
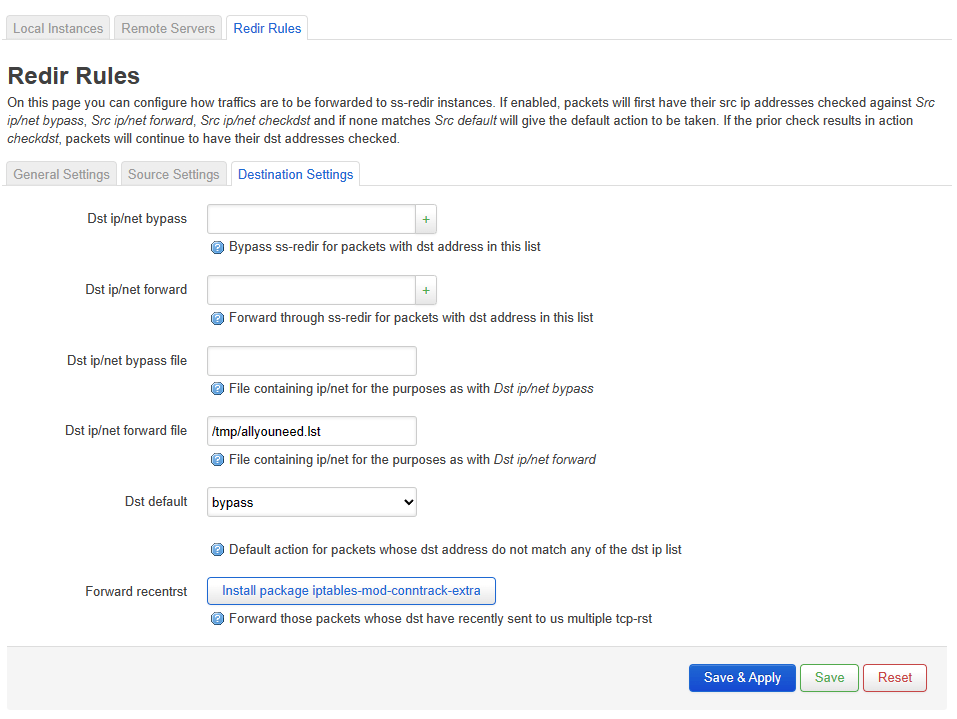
Click Save&Apply and check if it works.
Fixing the ss-redir error on OpenWRT 22.03 and higher:
The problem occurs due to incorrect default settings of Shadowsocks-libev conflicting with the updated firewall4 based on nftables and causing memory leaks and router freezes.
To fix it, you need to go to the Services section – Shadowsocks-libev – Redir Rules – General Settings
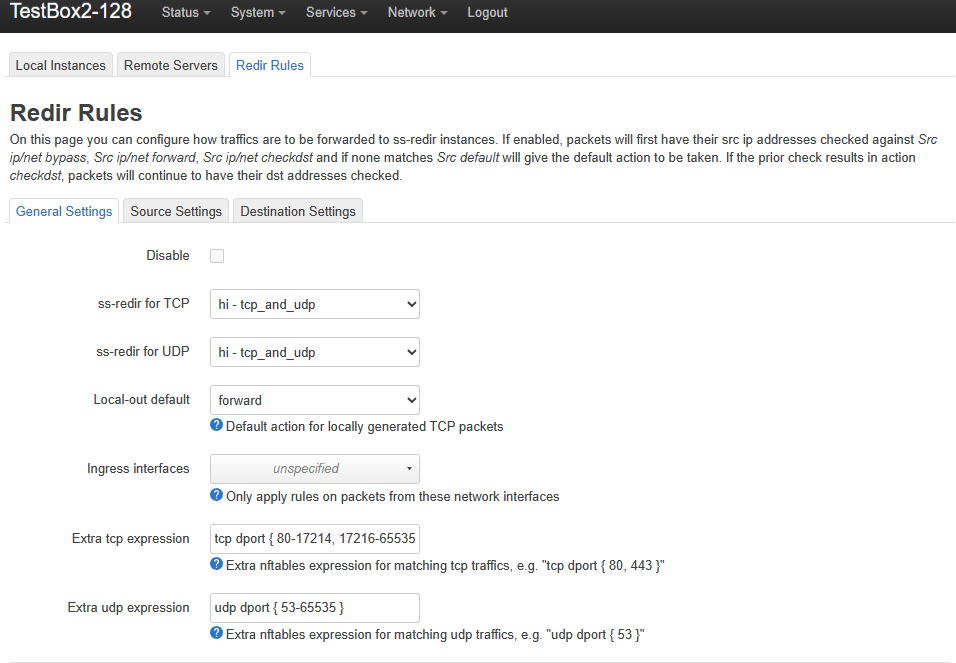
For the new version the following items must be completed:
Extra tcp expression – here the range of TCP ports routed through the proxy is indicated (even if these are all ports, they must be specified), fill in:
tcp dport { 80-17214, 17216-65535 } – in my case, the Outline port is 17215, I excluded it from the range, otherwise I get an ss-redir error. Be sure to write ranges taking into account your Outline port or leave the line – tcp dport { 80, 443 } so that only ports 80 and 443 are proxied.
Extra udp expression – here the range of UDP ports routed through the proxy is indicated (even if these are all ports, they must be specified), fill in
udp dport { 53-65535 } here I indicate all ports from 53 (DNS) to the last, there is no need to add the Outline port to exceptions, because shadowsocks works over TCP.
Save and Apply changes.
This is enough for shadowsocks-libev to work on OpenWRT 22.03 and higher.
Leave a comment